Funded Research Grants
Machine Learning for Countering UAV-Swarms
Agency: ARO
PI: Sanjay Madria
Amount: $500,000
Time period: 10/2022 - 09/2025
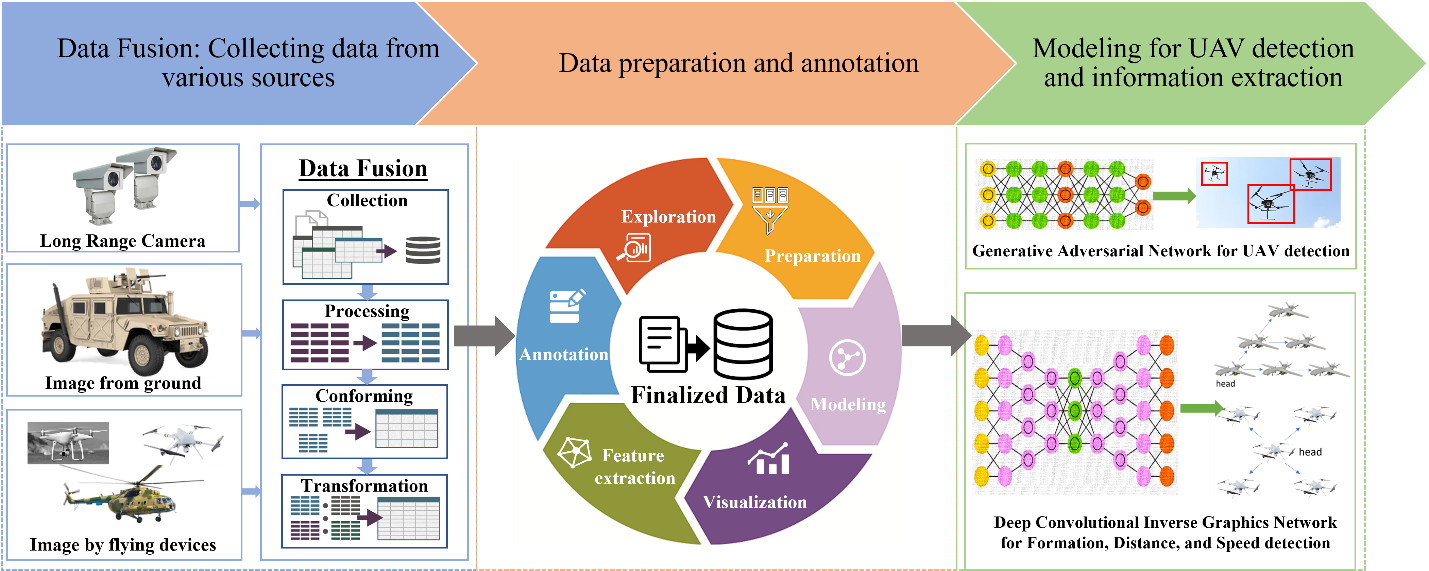
The proposed research objective is to detect UAVs from images taken by aircraft, ground vehicles, or persons by applying machine learning models. The many different types of UAVs, such as micro-UAVs, large combat UAVs, GPS UAVs, High Altitude Long Endurance UAVs, etc., can be differentiated by their visual looks. Efficient detection and identification of them can provide probable motives/missions and how much priority should be given to them. A series of images of the UAVs can indicate velocity (direction and speed) but this approach has multiple challenges. First, images are taken from different distances and resolutions and hence the distance of the UAVs from the camera is estimated rather than fully known. Second, UAVs moving as, or within swarms/teams, have different formations when performing a group task which complicates inference. Third, relative motion between the camera, the target, and the surrounding scene can cause a significant and high-dynamic variation in illumination conditions, background characteristics, and target appearance. Therefore, three important detection cases and techniques are posed as the sub objectives: (1) To identify the UAV distance by detecting their size proportion in an image and their type with the actual size of a UAV; (2) To detect the formations of the UAVs as a group; and (3) Identification and classification of UAV by using radio frequency and electromagnetic emissions.
CRII: CIF: Sequential Decision-Making Algorithms for Efficient Subset Selection in Multi-Armed Bandits and Optimization of Black-Box Functions
NSF
Award amount: $174,982
Time Period: 05/01/23 to 04/30/25
Unlike fixed decision-making algorithms, sequential decision-making (SDM) algorithms are often more efficient in the number of samples needed to solve a problem. Obtaining additional samples can be expensive and time-consuming. Consequently, SDM algorithms have been used in a wide range of applications ranging from recommender systems and automated drug discovery to the tuning of parameters in engineering design models. This project will develop new algorithms that enhance the applicability of SDM and improve its efficiency. Performance guarantees for the algorithms will be obtained and they will be tested in real-world data experiments. The project outcomes can lead to increased use of SDM in industry sectors such as e-commerce and drug design. The project will provide research opportunities for a diverse group of students and the knowledge gained will be integrated into the university’s graduate curriculum and will broaden the K-12 outreach activities undertaken by the investigator.
The project is organized under two problem frameworks: subset selection and black-box optimization. In the first problem of subset selection, the objective is to select a good subset among many alternatives. This objective is formulated as a subset selection problem in multi-armed bandit models. The project will develop SDM algorithms that obtain a good subset using the gaps between consecutive arm means. This removes the need to specify a parameter that defines the good subset. The SDM algorithms will exploit arm features in linear multi-armed bandit models and the theoretical analysis will obtain sample complexity bounds for the proposed algorithms. In the second problem of black-box optimization, such arm features are not available, and partition-based optimization methods are often used. This project will develop SDM algorithms that adapt the partitioning scheme to the black-box function being optimized. Convergence to the optimal value will be ensured and their practical performance on benchmark simulations will be measured. The outcomes of the project will be communicated in papers and the developed code will be made publicly available.
CRII: FET: New Theoretical Foundations for Quantum Walks with Applications
PI: Avah Banerjee
NSF
Award amount: $175,000
Time Period: 02/08/23 to 02/08/25
In principle, quantum algorithms can perform certain computational tasks faster than any known classical algorithms. However, the postulates of quantum mechanics underpinning quantum algorithms, create unique challenges that need to be overcome in order to expand their applications. This project investigates the power and limitations of quantum walks, which is a quantum analogue of classical random walks. Quantum walks have been used in state-of-the-art quantum algorithms; from finding a marked vertex in a graph to simulation of quantum systems. Despite this, the dynamical behavior of the “quantum walker” is not well understood, which can be highly non-trivial due to its wave-like interference properties. This makes it difficult to effectively guide the propagation of the “quantum walker” when the underlying geometry of the search problem is complicated. The primary aim of this project is to develop mathematical and algorithmic tools to broaden our understanding of quantum walks. Through education, curriculum development and outreach activities, the project will also contribute towards training an interdisciplinary cohort of students in quantum computing. Further, this project will foster research across mathematics (group and representation theory, simplicial homology, graph theory), physics (scattering theory, quantum walks) and computer science (property testing, subgraph finding).
Expanding the applications of quantum walks poses several challenges. First, it is difficult to derive analytical expressions for the resulting distribution of certain important classes of quantum walks, even on highly symmetric graphs. This is due to the presence of destructive interference. Second, we do not have a good understanding of when quantum walks can lead to super-polynomial or exponential speedup. Third, apart from a few carefully constructed examples, we do not know how to apply quantum walks to find or detect non-trivial subgraphs of a given graph. To overcome some of the above obstacles, this project undertakes a systematic study of quantum walks as a generative model for non-trivial distributions on vertices and edges of graphs and their higher dimensional extensions such as simplicial complexes (SC). The resulting theory will be used in testing certain properties of and finding complex sub-structures within these objects. More specifically, the following topics will be investigated: dynamics of quantum walks on non-abelian Cayley graphs and SCs with certain cohomologies, applications of quantum walks for property testing and search problems on SCs, and connection between scattering quantum walks and the symmetries of the underlying graph.
Machine Learning for Countering UAV-Swarms
Agency: ARO
PI: Sanjay Madria
Amount: $500,000
Time period: 10/2022 - 09/2025
The proposed research objective is to detect UAVs from images taken by aircraft, ground vehicles, or persons by applying machine learning models. The many different types of UAVs, such as micro-UAVs, large combat UAVs, GPS UAVs, High Altitude Long Endurance UAVs, etc., can be differentiated by their visual looks. Efficient detection and identification of them can provide probable motives/missions and how much priority should be given to them. A series of images of the UAVs can indicate velocity (direction and speed) but this approach has multiple challenges. First, images are taken from different distances and resolutions and hence the distance of the UAVs from the camera is estimated rather than fully known. Second, UAVs moving as, or within swarms/teams, have different formations when performing a group task which complicates inference. Third, relative motion between the camera, the target, and the surrounding scene can cause a significant and high-dynamic variation in illumination conditions, background characteristics, and target appearance. Therefore, three important detection cases and techniques are posed as the subobjectives: (1) To identify the UAV distance by detecting their size proportion in an image and their type with the actual size of a UAV; (2) To detect the formations of the UAVs as a group; and (3) Identification and classification of UAV by using radio frequency and electromagnetic emissions.
REU Site: Research and Training Experience for Undergraduates in the Areas of Cybersecurity, Data Analytics, and Blockchain for Securing Big Data and Cyber-Physical Systems
PI: Sanjay Madria
CO PI: Sajal Das & Sid Nadendla
Amount: $462,000
Time period: 04/2022 - 03/2025
This award is to set a new site for Research Experiences for Undergraduates (REU) in the Computer Science Department at the Missouri University of Science and Technology. Each summer a cohort of undergraduate students will visit Missouri S & T campus to work with faculty in small groups to design, implement, and evaluate research projects involving Cybersecurity, Data Analytics, and Blockchain for securing systems such as Cyber-physical Systems. The site will focus on recruiting under-represented and women students from diverse groups in computing fields from 2 to 4-year institutions. The students will participate in professional development activities that make them more aware of graduate school and professional aspects of a computing career. The students will be able to use the state-of-the-art facilities available at the university and interact with faculty mentors to conduct challenging and timely research on emerging technologies to develop secure systems for the future.
This new REU Site at The Missouri University of Science and Technology will focus on research projects involving Secure Data Sharing Scheme for Cloud, IoT Access Control Using Permissioned Blockchain, Security and Trustworthiness in Data-Driven CPS and IoT and Crowd-Audit in ML-based Systems. The use of cybersecurity across different domains and technology offers an effective means for establishing secure cyberinfrastructures across a wide variety of applications thus, contributing toward a technology-based society. REU students, postdocs, graduate students, and faculty will have the opportunity to explore problems that are important and timely, and relevant to our society. This project will also build human capacity in cybersecurity, machine learning, CPS, and IoT research and knowledge. The program will provide experiences to undergraduate students that may influence their choices about further education and future careers and continue to give them the confidence to pursue these choices and thus, increase the size and diversity of the scientific workforce.
This site is supported by the Department of Defense ASSURE Program in partnership with the NSF REU Program.
CNS Core: Small: FLINT: Robust Federated Learning for Internet of Things
PI: Tony Luo
Co-PI: Sajal Das
Amount: $500,000
Time period: 10/1/2020 - 09/30/2023
Federated learning enables machine learning on distributed datasets without needing the learner to access directly the datasets owned by respective stakeholders. The Internet of Things (IoT) provides a fertile ground for applying federated learning, where distributed IoT devices produce a plethora of data that are often private. However, IoT devices are vulnerable to environments with inaccurate data samples and malicious attacks, which is a significant challenge for federated learning. Agglomerating data in a federated and robust manner may produce benefits to the economy and society.
Objectives of the Robust Federated Learning for Internet of Things (FLINT) project include: (1) Formulate federated learning (FL) in heterogeneous, dynamic IoT environments with unreliable and adversarial clients. (2) Design new FL algorithms that are robust against hostile conditions with benign, unreliable, and malicious clients injecting erroneous or poisonous data. (3) Design novel incentive mechanisms to ensure rational clients gain non-negative utility by contributing training data and resources. (4) Analyze complexity, performance, and theoretical bounds of proposed algorithms. (5) Build an IoT testbed to study the learning performance of robust FL solutions. (6) Simulation experiments on real-world datasets to evaluate performance scalability.
The FLINT project will offer graduate and undergrad students a unique opportunity to gain interdisciplinary education in the design of robust FL algorithms for IoT. Research findings will enrich courses on cyber-physical systems and machine learning for IoT.
Secure Monitoring and Reconnaissance for CBRN and other Threats
Sole PI: Sanjay Madria
Amount: $215,000
Time period: 10/2021 - 08/2023
In this proposal, the focus is to enhance Chemical, biological, radiological, and nuclear defense (CBRN) reconnaissance capability to detect and track CBRN hazards on the move without transmitting GPS data, which increases the survivability of CBRN reconnaissance forces. It also integrates machine learning into CBRN reconnaissance platforms, increasing the quality of service (QoS), privacy, and capability to conduct continuous monitoring and reporting in real-time. The objective of this proposal is to design, develop and demonstrate trajectory-based data access control protocol for GPS-free information detecting and dissemination to enable real-time target tracking, CBRN hazards marking, and real-time remote control. As the battlefield environment requires minimal radio footprint and maximum local anonymity, we aim to eliminate the location information in all the radio communication while still allow different groups of forces to share the trajectory of CBRN intelligence.
GAANN: A Doctoral Program in Big Data, Machine Learning, and Analytics for Security and Safety
PI: Sanjay Madria Co PI's: Jagannathan Sarangapani
Sajal Das
Award amount $640,000
Award date: 10/1/18 to 9/30/23
This GAANN research program is to contribute toward the national need to address Big Data, Machine Learning and Analytics for Cyber Security and Safety in terms of Research, Education and Training. Big data is transforming science and engineering with applications in cyber security, infrastructure monitoring, and ultimately society itself. Global technological leadership in this area is important for the United States and can be sustained by educating future leaders. With new paradigms and technologies, big data and machine learning research continues with new innovative outcomes from both industry and academia. We recognize that one of the most effective means for designing, developing, and deploying big data systems and analytical solutions for cyber security is by making technical solutions and applications relatively quickly, while making these accessible to local and state entities as well as to the government in a timely manner. [Read more] [Dec 17, 2018]

Follow Computer Science